Secure file sharing and storage
The file sharing, storage and collaboration marketplace is crowded with applications promising to deliver on the potential of a ‘work anywhere, with anyone’, culture. However, not all of them offer encrypted file sharing.
Solutions like DropBox, Box and OneDrive all offer a degree of security but, for many organisations, they don’t meet their standards for maximum data protection.
SureDrop is different than the rest. Simple to use, it is also secure by design. It features strong encryption and data sovereignty control, without impacting on usability.
It is designed for organisations that have embraced remote working, but who also take security seriously.


The secure file-sharing app your IT department will approve of
- Allows people to store, share, sync and collaborate on all their files in one secure place.
- Supports all file types, sizes and formats and allows unlimited file copying for backup and recovery.
- Seamless integration with enterprise software applications, including Microsoft Azure Active Directory, Microsoft Outlook and Microsoft 365, makes single sign-on a breeze.
- Integrates with Votiro Secure File Gateway; for protection against the full range of malware.
- Flexibility of deployment as an on-premises solution or SaaS from the cloud.
- Customers are free to choose where they want their files stored to meet data protection regulations.
Designed to be better
Effortless file sharing without compromise
SureDrop provides all the tools and functionality you’ve come to know and love from solutions like Dropbox. We’ve simply added the surety of encryption security and data sovereignty control, so people who can’t use existing solutions can use SureDrop.
Enterprise software integration
By providing full compatibility with Microsoft Outlook and Microsoft 365, SureDrop enables simplified file collaboration and sharing, using the world’s best-known office suite. Integration with Microsoft Azure enables deployment as part of a broader PaaS or SaaS solution.
High performance and high availability
SureDrop delivers the highest possible resilience to a data network or device failure because it has designed-in fault tolerance and self-healing capabilities. SureDrop’s architecture and built-in redundancy minimise the inconvenience of communication failures. This ensures your files are always available and in sync.
Flexible deployment
SureDrop is available as an on-premises, SaaS or managed service provider solution. However, you choose to deploy your solution, SureDrop’s security features are the same.
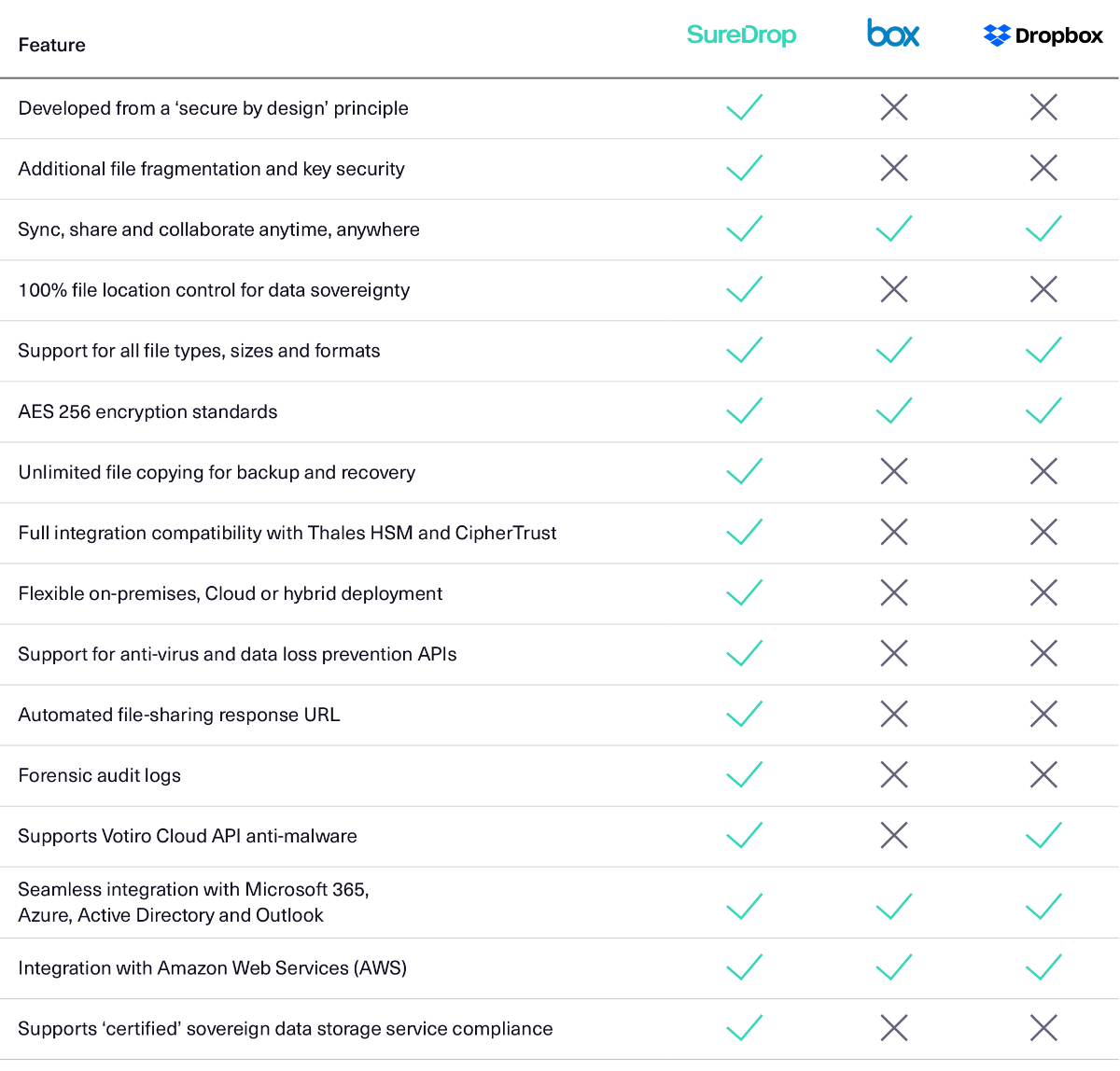
SureDrop features comparison
Designed to mitigate business risk
- Avoid loss of reputation and financial penalties over data breaches: Provides security for personally identifiable, confidential or high-value information, that needs to be kept safe.
- Ensure compliance obligations are met: Meets the security standards required by industry regulations or internal IT policies, that many public file sharing services do not.
- Keep hybrid working secure: Enable secure file sharing, storage and collaboration across private and public infrastructure, plus a wide range of user-owned devices.
- Ensure data protection laws are regulations are being met: Data protection mandates may dictate where your data is held. SureDrop provides 100% control over file location.
Made with customer concerns in mind
Standards-based Encryption
AES 256bit standards-based encryption algorithms provide maximum data security.
100% control
With SureDrop, you have complete control over your data location; providing data sovereignty compliance.
Maximum File Security
State-of-the-art, zero-touch encryption key management. Seamless integration with Thales HSM provides maximum key storage security.
Seamless Management
The SureDrop client is remotely deployed using a silent install option and automatically updates as required, without IT intervention.
A Fully Antonomous Solution
SureDrop is fully self-governing and does not require external appliances to generate or distribute the encryption keys.
Anti-Virus and DLP
SureDrop supports both anti-virus and data loss prevention (DLP) software APIs.
Unlimited file size and type
Unlike some file sharing applications, SureDrop places no limits on the size or type of file you can upload.
100% Redundancy
SureDrop enables unlimited file copying. Whatever your policy for backup and recovery, it automatically copies files to
the correct location.
Effortless Integration
SureDrop integrates seamlessly with your enterprise architecture, or that of your communications service provider.
Highly Resilient
SureDrop delivers exceptional resilience; thanks to designed in fault tolerance and self-healing capabilities.
Key features
For organisations taking cybersecurity seriously
Robust, standards-based encryption
SureDrop is different because it has been designed and built from the ground up using defence-grade encryption security. In addition to using standards-based AES256 bit algorithms, SureDrop utilises file fragmentation for an extra layer of security.
State-of-the-art encryption key management
SureDrop gives you peace of mind that your encryption keys cannot be accessed by anyone but you. Senetas encryption key management delivers 100% control of your encryption keys. Your IT department is free to implement and manage the most stringent key storage security.
Malicious content protection
For the additional peace of mind that comes from malicious content protection, SureDrop is available with the Votiro Secure File Gateway extension. Votiro leverages patented technology to protect your files from the most advanced, persistent cyber-attacks and malware.
Secure key management
SureDrop provides simple and secure encryption key management across the entire lifecycle; including key generation, storage, distribution and deletion.






